jmanteau
Mon coin de toile - A piece of Web
The Rise of Immutable Linux Distributions
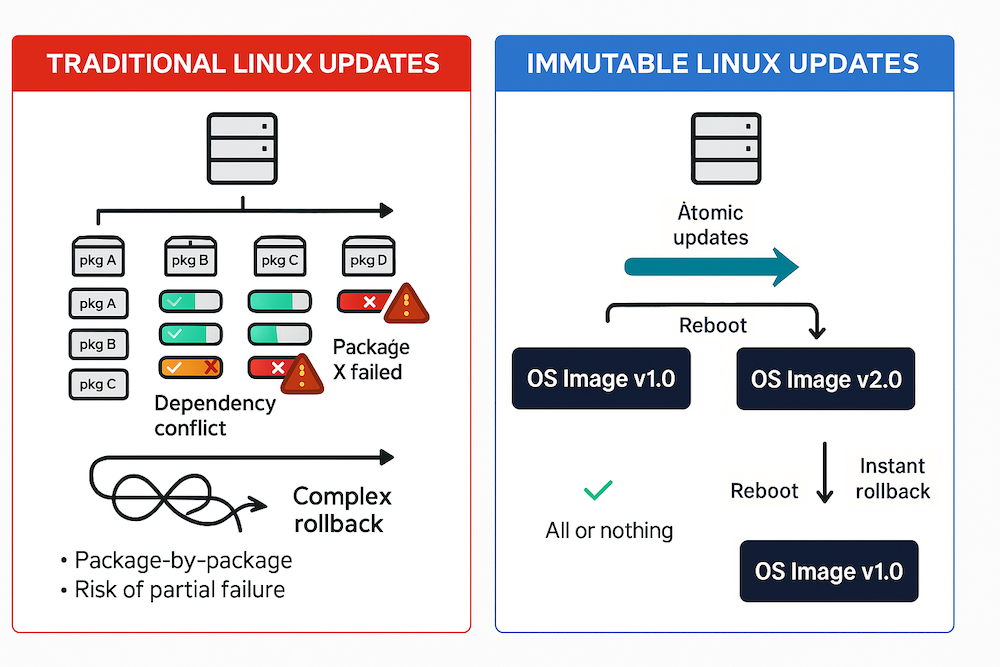
Since the 2010s, the concept of immutable Linux distributions has steadily gained traction. This shift closely followed the rise of container technologies (particularly Docker) which prompted the industry to rethink how Linux systems should be built, maintained, and secured. Unlike traditional systems that rely on mutable filesystems and incremental package updates, immutable systems treat the OS as a single, read-only image that is updated atomically, not incrementally.
At Red Hat Summit 2025, Chris Wells (RHEL Product Marketing) summarized the shift:
The patch-and-pray model is broken. Immutable systems treat the OS like a container: consistent, testable, and fully revertible. That’s what sysadmins want—predictable, simple, reliable.
Immutable OS updates align with DevOps practices: CI-tested images, reproducible builds, and streamlined rollbacks.
I. What Is an Immutable Linux Distribution?
Immutable distributions lock the core system (kernel, libraries, system tools) as read-only. Updates are performed by replacing the entire image in a single transaction, usually requiring a reboot. If an issue arises, administrators can roll back to a previous known-good state simply by rebooting into the prior system image. It allows immediate operation recovery without manual rollback actions at system level.
This architecture enhances reliability, simplifies recovery, and improves resistance to system corruption and unauthorised changes.
II. Why Embrace Immutability?
-
Security: The root filesystem is mounted as read-only, eliminating many vectors for persistent compromise. Unauthorized modifications are blocked outright, and system integrity is preserved across reboots. Combined with cryptographic verification of image signatures, this model strengthens the trust boundary at the OS level.
-
Consistency at Scale: All systems booting from the same image exhibit identical behavior, eliminating the class of bugs caused by configuration drift or package version mismatches. This consistency streamlines troubleshooting and enables confidence in fleet-wide changes.
-
Atomic Upgrades and Rollbacks: OS updates are delivered as monolithic, versioned images. No partial updates, no broken dependencies. If an upgrade fails, the system can revert to a known-good state with a reboot, reducing downtime and eliminating the need for complex rollback procedures.
-
Container-Native Architecture: Immutable hosts are well-suited for running containers. Applications are deployed in isolated, reproducible environments, with the host system acting as a stable substrate. This aligns with DevOps and GitOps workflows (reduces operational overhead, improves security boundaries).
III. Real-World Adoption
Immutable distributions excel in Kubernetes nodes, edge computing, fleet deployments, and any scenario requiring guaranteed consistency across hundreds of identical systems.
Major adopters include automotive companies using Fedora CoreOS for connected vehicles, financial institutions running RHEL CoreOS for trading systems, and cloud providers deploying Flatcar for their Kubernetes infrastructure.
The common thread: environments where system drift is unacceptable and rollback capability is critical.
IV. Pioneers and Ecosystem Evolution
CoreOS (2013) was the first major immutable Linux, optimized for container workloads and Kubernetes clusters. It set the foundation for later Red Hat projects :
-
Fedora CoreOS: Headless server OS with OSTree, rpm-ostree, auto-updates, and container-native design.
-
Fedora Silverblue: Immutable desktop OS using Flatpak for apps and ostree for OS image management.
-
Red Hat Enterprise Linux 10 (RHEL 10): the first RHEL release to offer image-based deployments as a supported option alongside traditional RPM-based systems. Using “bootc” technology, it allows to choose between traditional or immutable deployment models based on the needs.
Other notable distributions:
-
Flatcar Container Linux: A direct successor to CoreOS.
-
Ubuntu Core: Transactional updates and minimal base.
-
Chainguard OS: Focuses on supply chain security and minimal attack surface.
V. Core Technologies for Immutability
1. OSTree: Git for Operating Systems
OSTree (libostree) provides the foundation for many immutable Linux distributions. It manages bootable, versioned filesystem trees through a content-addressed object store similar to Git.
OSTree stores files by their checksums, which enables deduplication across versions. System updates prepare offline and switch atomically at boot time. Files unchanged between versions share storage through hardlinks. Previous deployments stay available for rollback if needed.
/ostree/
├── repo/ (deduplicated content store)
└── deploy/
└── fedora/
├── deploy/12345.0/ [ACTIVE] ←── Current boot
├── deploy/12345.1/ [STANDBY] ←── Previous (rollback available)
└── deploy/12345.2/ [STAGING] ←── New update preparing
OSTree creates read-only bind mounts for system directories like /usr. Writable areas such as /etc and /var remain separate. This separation keeps the core OS immutable yet permits required runtime modifications.
2. A/B Partitioning
A/B partitioning implements immutability at the hardware level. This approach appears frequently in embedded systems and Android devices.
[Boot Partition]
[System A Partition] <- Active
[System B Partition] <- Inactive (for updates)
[Data Partition] <- Persistent user data
The system runs from partition A during normal operation. Updates write to the inactive partition B without affecting the running system. The bootloader configuration changes to point to partition B. After reboot, the system runs from partition B. Partition A then becomes available for the next update cycle.
This method provides complete isolation between the running system and updates. Rollback occurs instantly by switching the boot partition. No intermediate states exist during the update process.
3. Btrfs Snapshots
Btrfs (B-tree filesystem) implements snapshot capabilities that support immutability at the filesystem level.
The Copy-on-Write mechanism creates new blocks for modifications instead of overwriting existing data. Snapshots are created almost instantly with minimal overhead. Subvolumes function as independent filesystem roots within a single btrfs filesystem.
# Create snapshot before system update
btrfs subvolume snapshot -r / /.snapshots/pre-update
# Perform update
dnf upgrade
# If issues arise, restore from snapshot
btrfs subvolume delete /
btrfs subvolume snapshot /.snapshots/pre-update /
openSUSE MicroOS implements btrfs snapshots with a read-only root subvolume. Updates occur transactionally by creating new snapshots. The Snapper tool manages snapshots automatically based on configured policies.
4. OverlayFS
OverlayFS creates a union filesystem by stacking one filesystem over another. This technique permits temporary modifications to read-only base systems.
┌─────────────────────────┐
│ Merged View (/) │ ← What users see
├─────────────────────────┤
│ Upper Layer (R/W) │ ← Modifications
├─────────────────────────┤
│ Lower Layer (R/O) │ ← Immutable base
└─────────────────────────┘
Container systems like Docker and Podman implement overlayfs for container image layers. Live systems use it for temporary modifications to read-only media. Development environments apply it when testing changes without modifying the base system.
mount -t overlay overlay \
-o lowerdir=/readonly/base,\
upperdir=/writable/upper,\
workdir=/writable/work \
/merged
5. rpm-ostree Layering
rpm-ostree merges OSTree’s image-based approach with RPM package management. This combination permits controlled modifications to immutable systems.
The base image consists of an immutable OSTree commit containing the core OS. Package layering adds RPMs on top of this base. Client-side composition combines these layers locally into a new deployment.
# Install additional package on immutable system
rpm-ostree install docker
# System creates new deployment with package
# Reboot required to activate
# Remove layered package
rpm-ostree uninstall docker
# View current layers
rpm-ostree status
This approach maintains immutability yet permits customization. Operations remain atomic with rollback capability. The base OS stays distinct from user additions.
VI. Drawbacks and Limitations
While immutable systems offer strong benefits in consistency and security, they also impose structural and operational constraints that require adjustment.
-
Reduced Flexibility / Operational Rigidity: On-the-fly system changes are not well supported. All modifications, whether patching, configuration changes, or package additions, must be implemented through a new image and deployed via controlled pipelines. Some systems, like OSTree, allow emergency fixes but they will disappear at the next reboot. It demands greater discipline in managing system state.
-
Reboot Dependency: Because updates and rollbacks are tied to full image replacements, changes generally require a reboot. This complicates uptime guarantees and makes patch orchestration more demanding in high-availability contexts.
-
Cultural and Workflow Shift: Admins must abandon familiar tools and practices (e.g., direct package management, in-place editing) in favor of image-based workflows and declarative configuration. Image layering introduces new abstractions that require retraining and mindset shifts.
-
Ecosystem Tooling Gaps: Many existing monitoring, debugging, and automation tools were built for mutable systems and may not function as expected in an immutable environment. While the ecosystem is maturing, teams must often identify or build alternative tooling. Community and vendor support are improving but still uneven across the toolchain.
Conclusion
Adopting immutability means trading spontaneity for predictability. It rewards planned, disciplined operations and it penalizes improvisation. In sum, immutability enhances control, reliability, and reproducibility but at the cost of agility, especially for teams with dynamic or interactive operational needs. Success depends on adopting complementary practices (CI/CD, GitOps, structured image management) and reshaping expectations around change management.
The shift to immutability is not incremental: it is a paradigm change. RHEL 10, Fedora CoreOS, and others reflect a broader move toward treating infrastructure as code: repeatable, testable, version-controlled, and resilient by design.
Immutable Linux is no longer a fringe concept. It is becoming a standard model for building secure, scalable, and maintainable systems in the cloud-native era.